LYua
Bienvenue sur Lyua
Le blog pour les petits génies du web, passionnés de programmation et de développement
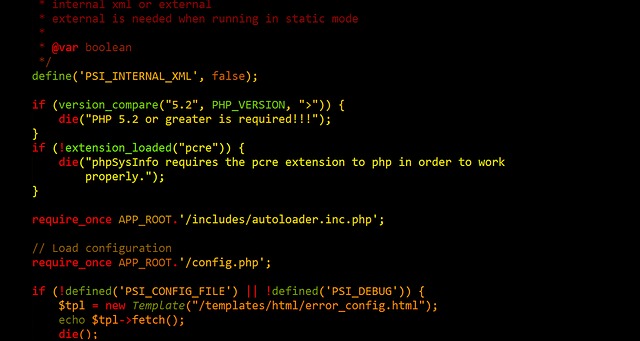
Tuto – créer sans coder ?
revoir les bases
Chaque développeur Web doit avoir une compréhension de base de HTML, CSS et JavaScript.
La conception Web réactive est utilisée dans tous les types de développement Web moderne.
ECMAScript 5 (JavaScript 5) est pris en charge dans tous les navigateurs modernes. Jetez-y un coup d’œil, en particulier les nouvelles fonctions de tableau.
Derniers articles
Le niveau superieur
Lorsque vous vous sentez à l’aise avec HTML et CSS, il est temps de creuser plus profondément.
Vous devriez apprendre à utiliser les cartes, les polices et les icônes en HTML.
Du côté JavaScript, vous devriez apprendre à accéder au DOM HTML.
Vous devez également apprendre à utiliser AJAX et JSON pour effectuer des requêtes serveur.
Tuto – Devenir développeur web
Cette vidéo vous présente comment on peut devenir développeur sans passer par des formations payante (il existe bien sûr d’autres méthodes)